The sound of the bubble from my Samsung tablet I keep in the living room notified me of an email. I set aside my teacup and checked my app.
I’ve had a couple of business transactions with Tobias Peerybingle a few years back. At the time, we exchanged emails had phone conversations and met face to face a couple of times a week. I haven’t heard from Toby since we completed our business at least 3 years ago.
The email that interrupted my evening tea, was from Toby. From out of the blue, Toby emailed me and informed me that a very important document is available on to Google Docs and that I should sign in with my email and read it. For a split second I contemplated clicking that link. After all, the email came from from someone I knew. Something about that email just didn’t seem kosher, thankfully I didn’t take the bait.
Malware – software that is designed to interfere with a computer’s normal functioning and that can be used to commit cybercrime (as by revealing passwords, PINs, and other sensitive data)
Read more: merriam webster definition
Had I clicked on the link and attempted to view the document, malware could have been installed on my system. The malware could attempt to look at my contact address book and send the same “you have a Google Doc” email to all my contacts. The email would appear to come from me but I would not be aware of it was even sent. The goal of malware, viruses, Trojan horses, etc is to steal passwords, your personal information; to steal your money one way or another.
How to defend against these cyber attacks.
- Think before you click – even if the email is from someone you know. Be especially wary of any emails that have attachments.
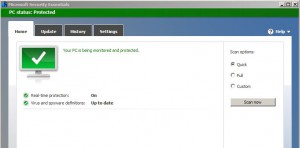
- Run virus protection software and keep it up to date. Decent virus protection comes with Microsoft Windows Security Essentials.
- Run firewall software such as Windows Firewall. A firewall blocks unauthorized access to your system and programs.
Other measures can be taken as well, the above items are a good start.